Our Services
Marketing services for cybersecurity companies
Specialist marketing designed for the trust-sensitive, technically sophisticated world of enterprise security — from compliance-focused SEO to CISO-targeted content and LinkedIn paid campaigns.
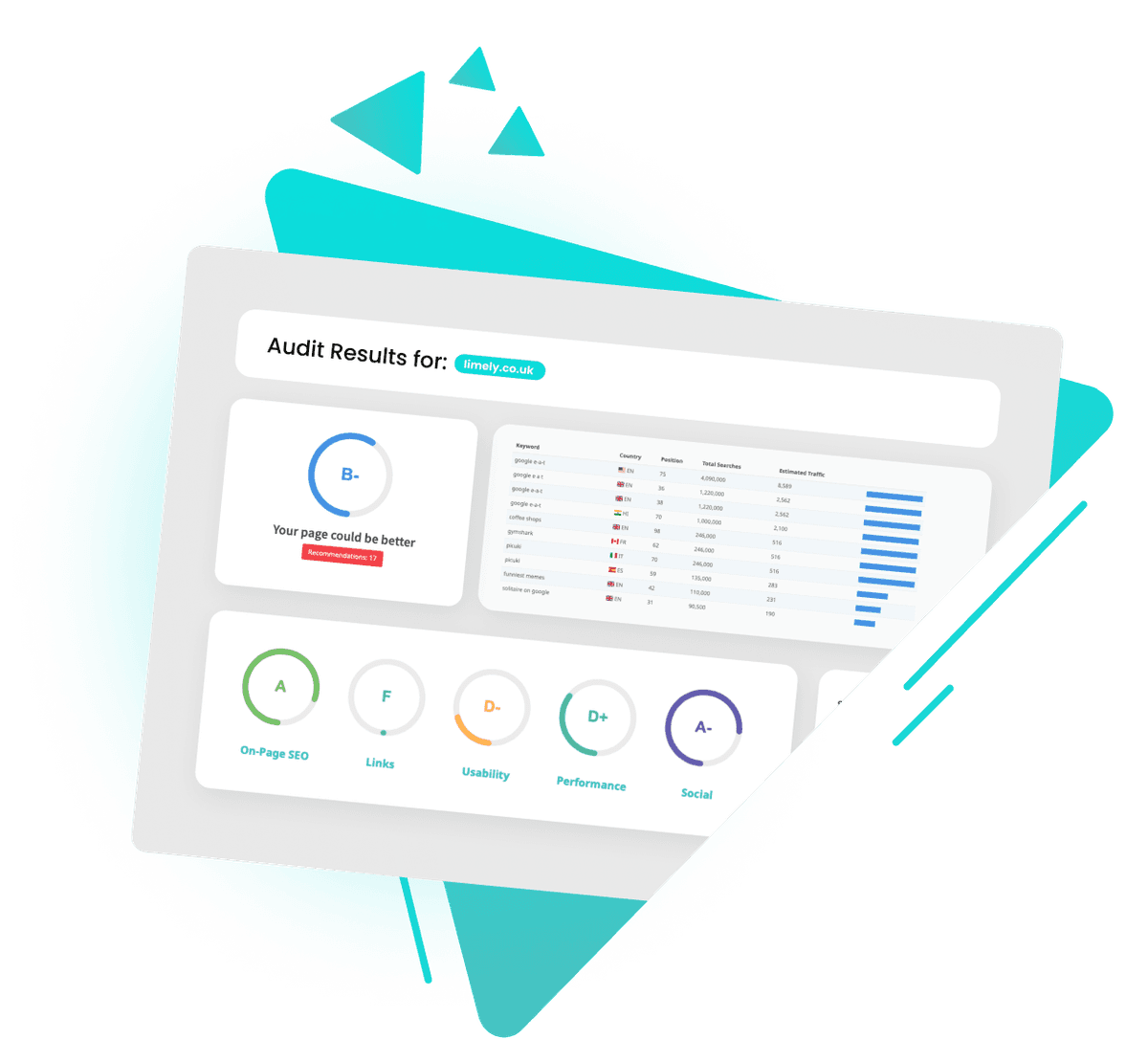
Security SEO
Rank for cybersecurity and compliance keywords
B2B Lead Generation
Qualified leads for enterprise security sales
Content Marketing
Technical content that demonstrates expertise
Thought Leadership
Position your team as security experts
Paid Campaigns
Target security decision-makers
PR & Media
Build credibility through industry coverage